We built Threat Zero Cyber because too many defense contractors and federal organizations are stuck in a compliance cycle that never closes. Firms identify gaps, hand over a spreadsheet, and disappear. The organization is left with findings and no path forward.
That ends today. We've rebuilt our platform from the ground up — a complete redesign focused on clarity, speed, and making it easier for organizations to understand exactly what compliance requires and how we get them there.
Our Mission
Every organization that handles federal data deserves a compliance partner that stays through remediation — not one that stops at the assessment.
What We Do
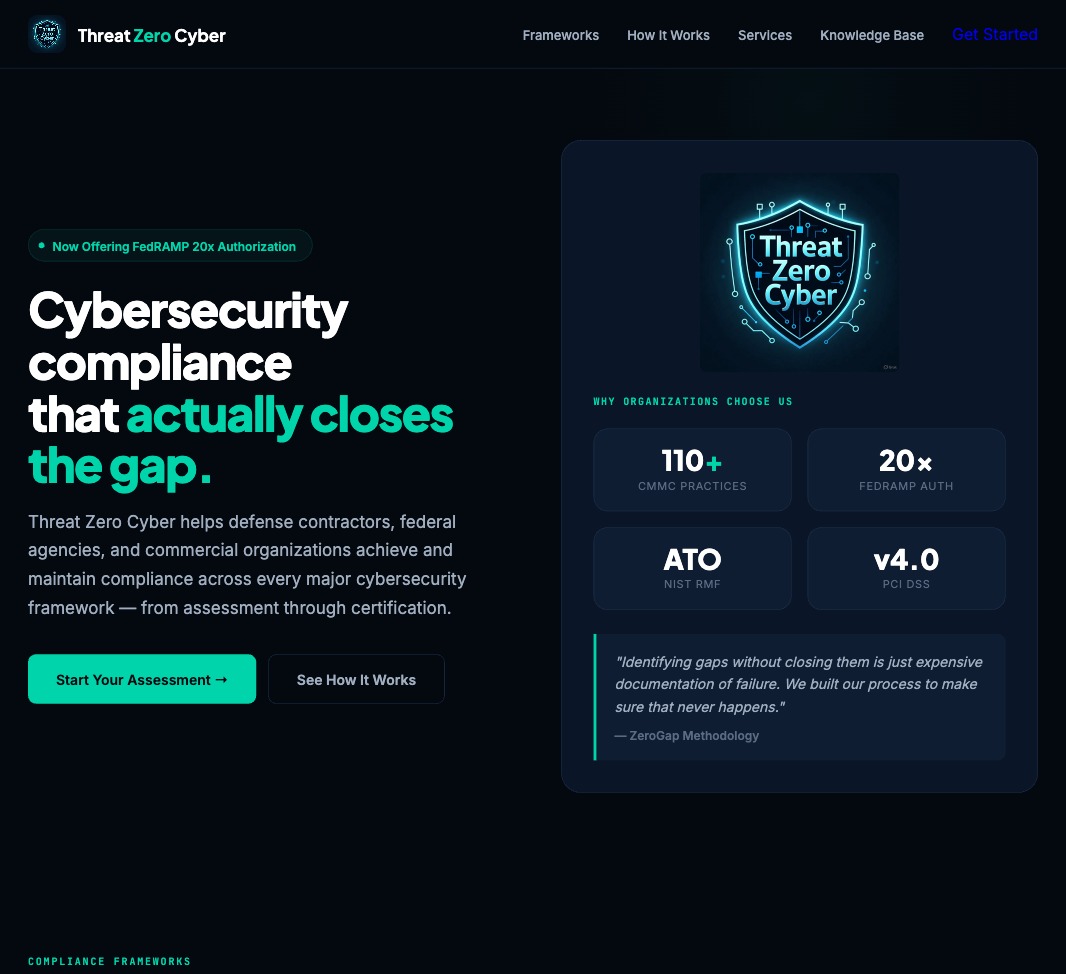
Threat Zero Cyber delivers full-lifecycle cybersecurity compliance for the defense industrial base, federal agencies, and commercial organizations operating in regulated environments. We don't just find gaps — we close them.
- Gap Assessments & RemediationPractice-by-practice analysis with findings tailored to your actual technology stack.
- Security EngineeringControl implementation, architecture hardening, and STIG alignment across hybrid and cloud environments.
- Penetration TestingInternal, external, and web application testing aligned to CMMC, FedRAMP, and NIST requirements.
- Policy & DocumentationSSPs, POA&Ms, risk assessments, and evidence packages built for assessor review.
- Certification ReadinessC3PAO preparation, 3PAO hand-off, FedRAMP agency sponsorship, and ATO package development.
- Continuous MonitoringOngoing compliance management, annual affirmation support, and sustained authorization programs.
- vCISO ServicesFractional security leadership with executive-level strategy, governance, and board reporting.
- GRC IntegrationTool configuration, policy lifecycle management, risk registers, and POA&M automation.
Frameworks We Cover
One methodology. Every major federal and industry cybersecurity framework.
The ZeroGap Methodology
Every engagement follows the same four-phase process — whether you're doing a CMMC Level 1 self-assessment or preparing for a FedRAMP authorization. The methodology scales to your organization.
Discover — We map your entire environment in plain language before a single practice is assessed. Tech stack, CUI boundaries, identity platform, endpoints, cloud services.
Analyze — Every interview question is built from your intake data. We reference your actual tools by name. Your SPRS score updates live with every practice decision.
Execute — Every NOT MET finding comes with prioritized remediation steps written for your specific tools. Auto-built POA&M with 90/180/270-day target lanes.
Deliver — Complete assessment package with scoring, domain heatmap, evidence checklists organized by assessment method, and a stakeholder briefing your leadership can act on.
Why Now
CMMC 2.0 is no longer theoretical. The final rule is published. Enforcement has begun. Defense contractors that aren't actively pursuing compliance are already behind.
FedRAMP 20x has fundamentally changed the authorization landscape, creating faster paths for cloud service providers willing to demonstrate real security outcomes.
Organizations need a partner that understands both the regulatory landscape and the engineering required to meet it. That's what we built Threat Zero Cyber to be.