Threat Zero Cyber - Trinity
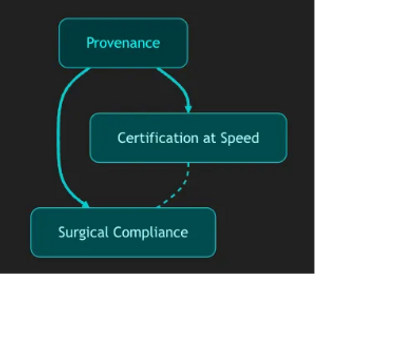
Threat Zero Cyber combines federal authority, surgical precision, and certification velocity to make CMMC NIST 800-171 , NIST RMF, PCI, and HIPAA compliance faster, cheaper, and audit-proof for defense contractors and commercial organizations
Threat Zero Cyber – Capabilities Overview
Risk Management Framework (RMF) Implementation & Support
End-to-end RMF lifecycle support for DoD/DoW, Civilian Federal, and contractor environments
System categorization, security control selection, implementation, and assessment
Continuous monitoring program development and automation integration
Authority to Operate (ATO) package development and validation support
FedRAMP 20x Authorization – The fastest path to FedRAMP Moderate and Low
CMMC Compliance Services
Readiness assessments aligned with CMMC 2.0 Level 1–3 requirements
Gap analysis and remediation planning for NIST SP 800-171 compliance
Continuous improvement and documentation support for audit readiness
Policy and procedure development to meet DFARS 252.204-7012 requirements
Governance, Risk, and Compliance (GRC) Integration
Tailored GRC tool configuration
Risk register creation, POA&M management, and reporting automation
Policy lifecycle management and continuous compliance alignment
Security Engineering & Assessment
Security control implementation across hybrid and cloud environments
Secure architecture design and hardening aligned with DoD/DoW STIGs and CIS Benchmarks
Penetration testing and vulnerability management tailored to RMF/CMMC baselines
Development of security technical implementation guides (STIGs) and baselines
UX/UI Design Services
Strategic user-centered UX/UI design and user research services grounded in over a decade of experience supporting federal agencies and private sector organizations. Apply a variety of user research methods such as interviews, usability testing, contextual inquiry, heuristic evaluations, and journey mapping, along with prototyping skills across low-, mid-, and high-fidelity web and application designs. Leverage expertise in accessibility best practices and design systems
Hands-on, end-to-end support across the full product development lifecycle, from discovery and research through design, prototyping, implementation, and continuous improvement. Apply practical, execution-focused expertise to help clients reduce risk, accelerate delivery, and deliver scalable, accessible, and compliant solutions aligned with user needs and organizational objectives. hands-on, end-to-end support across the full product development lifecycle, from discovery and research